在本文中,我们将演示使用Data Extractor来识别使用FileVault加密的Macintosh系统中的加密密钥位置。我们还将分享一些使用Data Extractor的技巧和方法。
In this article, we will demonstrate using Data Extractor to identify encryption key location in the Macintosh system encrypted with FileVault. We will also share some tips and techniques for using Data Extractor for maximum effectiveness.
我们注意到FileVault分区的加密密钥。
We started by exploring the ‘(Mac OS X) Boot Recovery HD’ disk for a while we noticed there was the encryption key for FileVault partition.
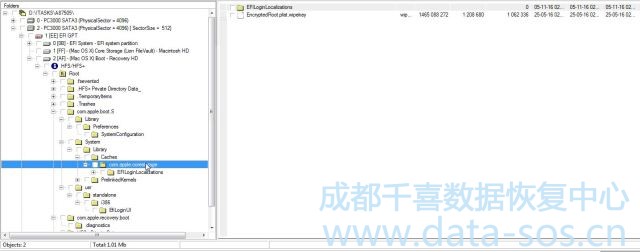
当我们输入FileVault分区的密码时,该密钥将被应用。名为’EncryptedRoot.plist.wipekey’,保存于’com.apple.corestorage’文件夹中。
This key is applied when we enter the password for FileVault partition. It’s called ‘EncryptedRoot.plist.wipekey’ and located in ‘com.apple.corestorage’ folder.
我们将这个文件保存到本地磁盘上
We were getting this file and saving in the special place on the local disk.
在某些情况下,该文件可以位于另一个地方或被删除。
For some cases, this file can be located in another place or be removed.
我们的目的是在我们输入加密分区的密码时上传这个文件,所以尽管我们不写这个文件,但是我们知道文件的确切名称,可以在另一个地方找到它。
Our goal is to upload this file when we enter the password for encrypted partition, so although we don’t where this file is written to, we know the exact name of the file and can find it in another place.
当文件被删除或分区格式化时,我们分别使用“扫描目录文件”选项或“分区分析”。
When the file was deleted or the partition was formatted we use ‘Scan Catalog file’ option or ‘Partition analysis’, respectively.
我们创建加密分区的映射。
We created a map of encrypted partition.
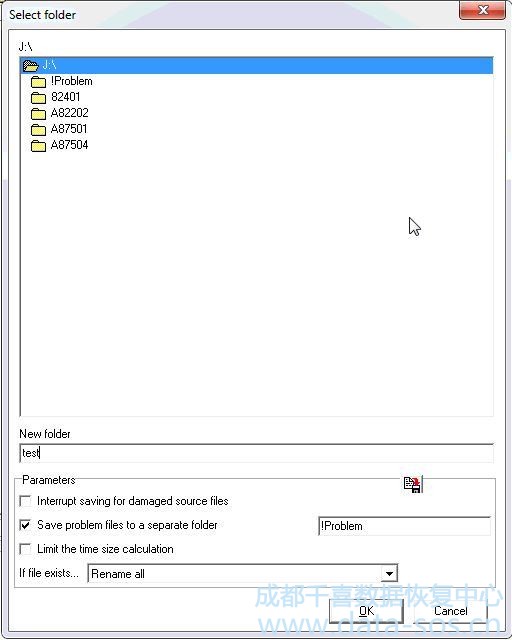
当您为加密的分区创建位图时,有一个重要的参数:Data Extractor要求您创建驱动器的子位图。它看起来像这样:
This is an important parameter when you create a map for encrypted partition: Data Extractor asks you to create submap of the drive. It looks like this:

关键在于,FileVault解密程序对扇区位置非常敏感。当我们创建驱动器的子映射时,扇区将被转移,而Data Extractor无法找到支持扇区并对分区进行解密。所以,我们的选择是“不”。
The point is that FileVault decryption procedure is sensitive to sectors location. When we create submap of the drive, sectors are shifted and Data Extractor can’t find support sectors and decrypt the partition. So, our selection is ‘NO’.
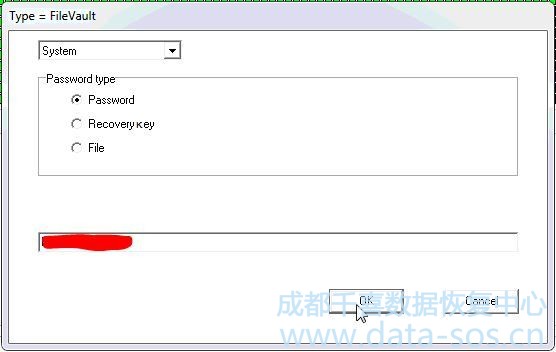
应用位图作为加密磁盘并输入密码。
Applied map as encrypted disk and enter the password.
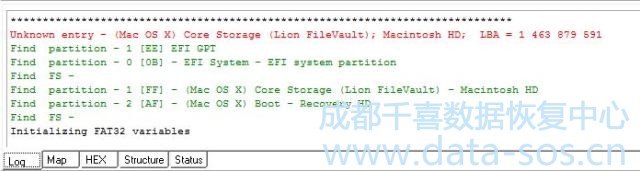
重新生成以下报告:
That regenerated the following report:
最后,我们得到的文件结构:
Finally, we were getting the file structure:
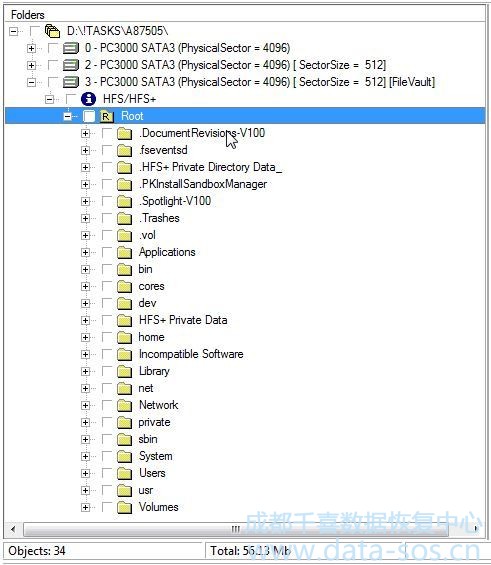
可以打开文件
And could open files:

Please keep your eyes on these features when you can’t decrypt FileVault partition using Data Extractor. It might not be a common issue but we hope it helped you in some cases.
数据恢复快乐
Happy data recovering!
转载请注明:成都千喜数据恢复中心 » 使用PC-3000 Data Extractor解密Apple FileVault实例